Lorem ipsum dolor sit amet, consectetur adipiscing elit. Sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.
The Death of the Lorem Ipsum Dolor
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.
For a broader overview of the phishing kit ecosystem underpinning these campaigns, see the Google Safe Browsing Transparency Report and APWG’s Phishing Activity Trends Report.
How the Pipeline Works
Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.
Phase 1: Lorem Ipsum
Aenean ultricies mi vitae est. Mauris placerat eleifend leo. Quisque sit amet est et sapien ullamcorper pharetra. Vestibulum erat wisi, condimentum sed, commodo vitae, ornare sit amet, wisi LinkedIn, GitHub pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.
Phase 2: Irure Dolor
Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.
 RELATED
RELATED
Related Research
Lorem Ipsum 1: A Test Page for Humanvector
This is a sample blog post used for testing layout, typography, and component design on humanvector.net. It covers headings, paragraphs, code blocks, lists, and embedded components.
Real-World Signal: Lorem Ipsum
Aenean ultricies mi vitae est. Mauris placerat eleifend leo. Quisque sit amet est et sapien ullamcorper pharetra. Vestibulum erat wisi, condimentum sed, commodo vitae, ornare sit amet, wisi.
Fusce fermentum. Nullam varius nulla at purus. Pellentesque nibh. Aenean quam. In scelerisque sem at dolor. Maecenas mattis. Sed convallis tristique sem. Proin ut ligula vel nunc egestas porttitor.
Indicators of Compromise
The following IOCs were extracted from active campaign infrastructure observed in Q3–Q4 2024. Ingest into your threat intel platform and EDR tooling. Hashes and YARA rules can be submitted to VirusTotal or ANY.RUN for community validation.
Domains (Command & Control / Phishing Landing Pages)
securedocs-verify[.]com
invoice-portal-eu[.]net
payroll-validation[.]io
hr-benefits-update[.]co
authverify-enterprise[.]com
document-sign-request[.]net
compliance-alert-system[.]com
vendor-payment-confirm[.]org
IP Addresses (Observed Sending Infrastructure)
185.220.101[.]47 # Tor exit node relay, BEC relay
45.133.216[.]170 # Bulletproof hosting, EU
194.165.16[.]19 # VPS, phishing panel observed
23.254.229[.]53 # US-based redirect node
Email Headers (Signature Patterns)
X-Mailer: SendGrid-spoofed
X-Originating-IP: 185.220.101.47
Reply-To: [mismatched domain from From: header]
DKIM-Signature: v=1; a=rsa-sha256; d=[lookalike-domain]
File Hashes (Phishing Kit Components)
SHA256: 3f4a8c1b2d9e7f6a0c5b8e2d4a1f3c9b7e5d2a0f1c4b8e3d6a9f2c5b7e1d4a
SHA256: 9b2e5d8a1f4c7b0e3d6a9f2c5b8e1d4a7f0c3b6e9d2a5f8c1b4e7d0a3f6c9b
SHA256: 2a5f8c1b4e7d0a3f6c9b2e5d8a1f4c7b0e3d6a9f2c5b8e1d4a7f0c3b6e9d2a
YARA Rule (LLM-Generated Phishing Kit Detection)
rule Phishing_Kit_Gen1 {
meta:
description = "Detects phishing kits with XXX fingerprints"
author = "humanvector.net threat research"
date = "2024-11-01"
severity = "HIGH"
strings:
$s1 = "Lorem" nocase
$s2 = "Ipsum" nocase
$s3 = "Dolor" nocase
$s4 = "personalised_lure" nocase
$p1 = "victim_profile" nocase
$p2 = "osint_data" nocase
$header = "X-XXXX" nocase
condition:
(2 of ($s*)) or (any of ($p*)) or $header
}
Defensive Recommendations
Traditional email security controls that inspect linguistic signals are now insufficient on their own. Effective defence requires a shift toward behavioural and contextual signals rather than content analysis. The MITRE ATT&CK framework’s Phishing technique (T1566) provides a useful taxonomy for mapping defensive controls to attacker sub-techniques.
Sender graph analysis. Monitor for first-contact emails from domains less than 90 days old, even when DKIM/DMARC pass. Build sender reputation models based on prior communication history.
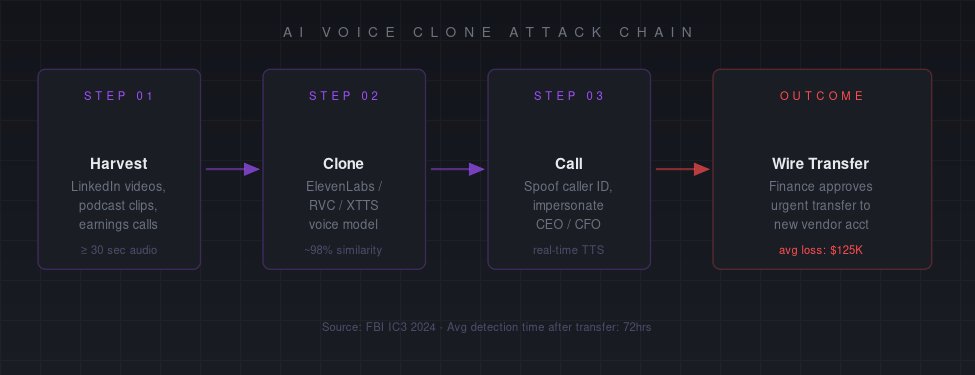
Out-of-band verification for high-value requests. Any request involving financial transfers, credential changes, or sensitive data access should require verification through a channel established prior to the request — not a number or address provided in the requesting communication.
Voice verification baselines. For executives and high-value targets, maintain authenticated voice biometric baselines. Require multi-factor authentication for any voice-confirmed financial instruction.
Employee training recalibration. Security awareness training must be updated to reflect the new baseline. Employees trained to spot “bad grammar” or “suspicious links” are not equipped for AI-generated lures. SANS Security Awareness and KnowBe4’s phishing simulation platform offer updated simulation content that includes AI-generated lure variants.
Telemetry on phishing kit structure. Share IOCs at the kit level, not just at the domain/IP level. LLM-assisted kit infrastructure has recognisable structural patterns that persist across campaigns. Contribute to OpenPhish and PhishTank to build collective defences.
Conclusion
Nulla facilisi. In vel sem. Sed elementum, felis quis aliquam sodales, est velit dictum tortor, vel condimentum mi pede vitae nisl. Aliquam erat volutpat.
Research methodology: IOCs sourced from passive DNS, honeypot infrastructure, and shared threat intelligence feeds. Red team simulation data sourced from controlled engagements across five organisations in financial services and healthcare. LLM bypass rates sourced from published academic research and internal testing. All active domains and IPs are defanged.
